Latest
-
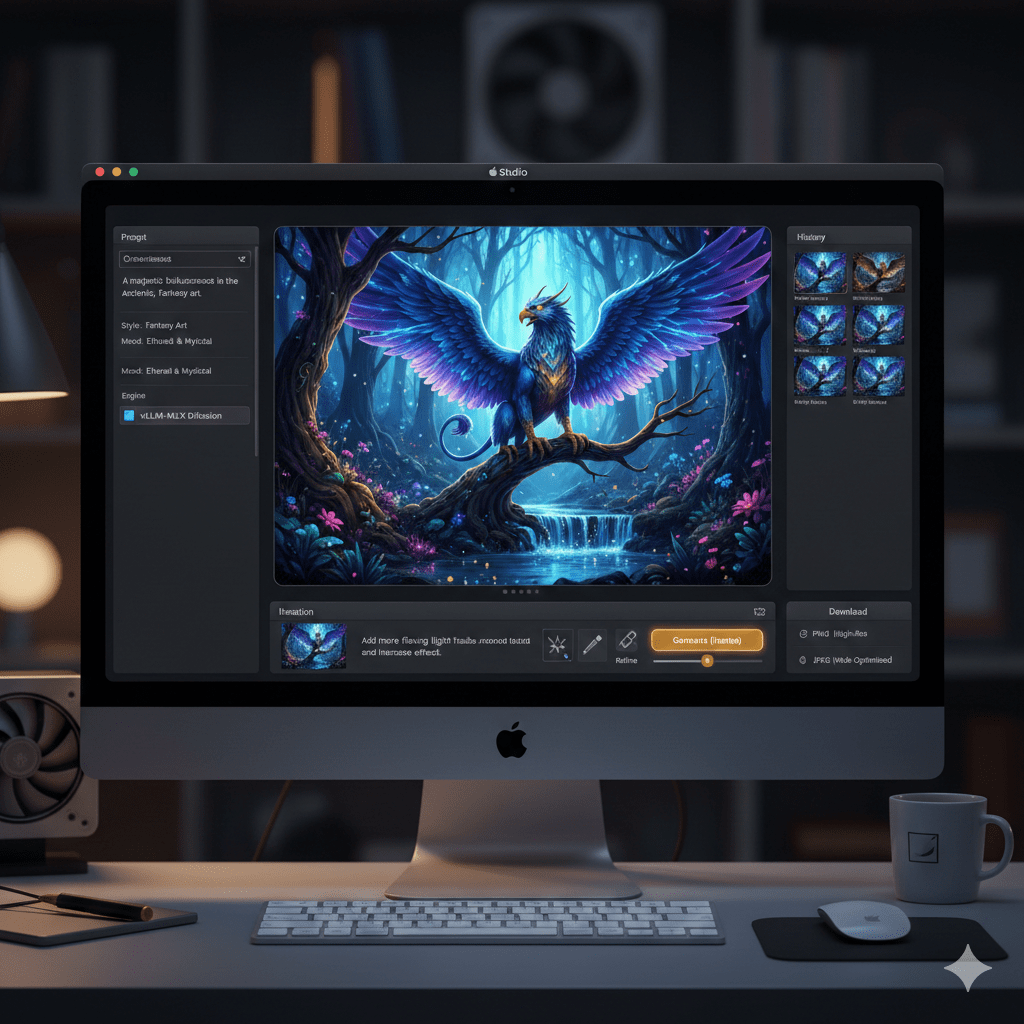
Running Your Own LLM Chat App on Apple Silicon with vLLM-MLX
A simple LLM chat application that runs entirely on your Mac, powered by vLLM-MLX, as a gentle introduction to the world of vLLMs.
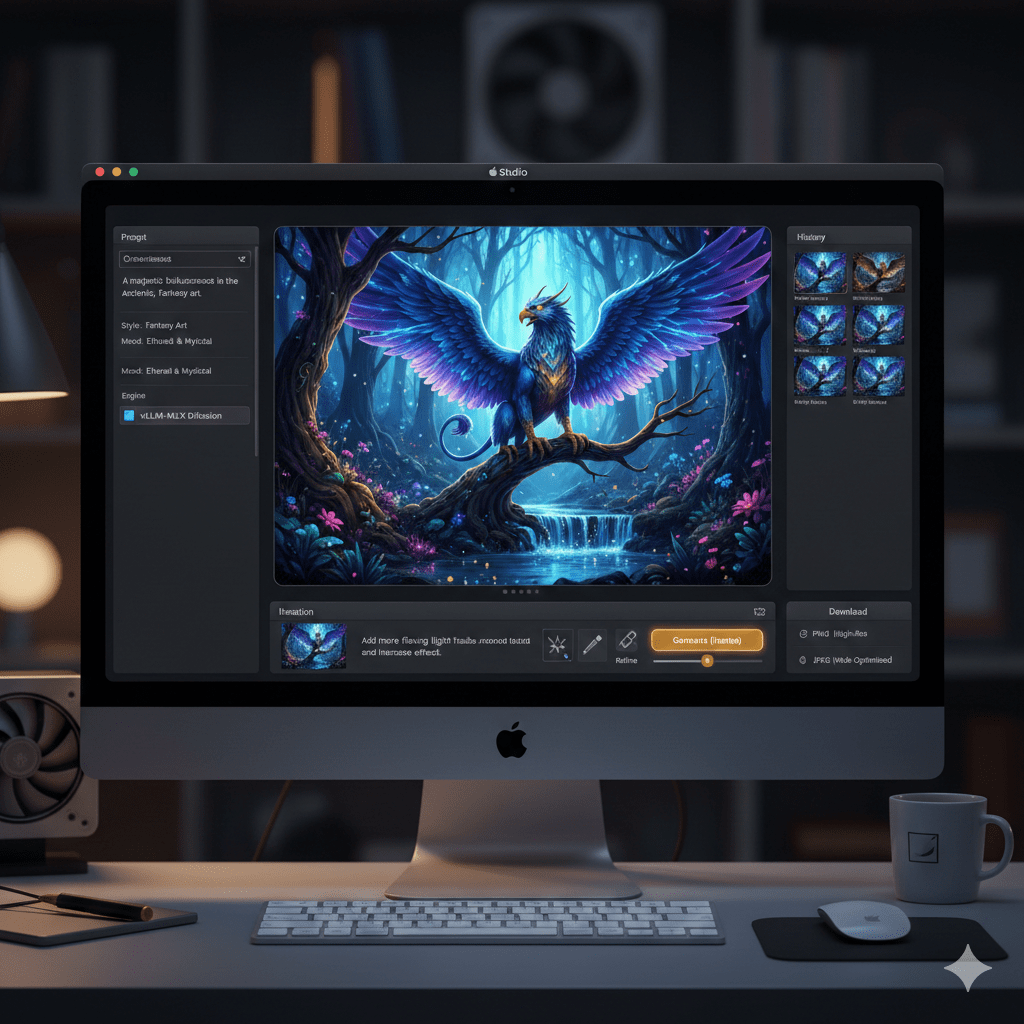
A simple LLM chat application that runs entirely on your Mac, powered by vLLM-MLX, as a gentle introduction to the world of vLLMs.